Managed service providers (MSPs) are an important and growing element of the technology
industry, providing businesses with a wide range of IT services, from data and application
management to networking and user support. MSPs can help businesses with everything
from basic IT systems to complex cloud computing solutions.
MSPs: Adopting Cyber Solutions to Better Serve their Clients
By Andrew Ruth on May 31, 2023 9:00:17 AM
Building A Successful Hybrid Workforce
By Greg Marts on Apr 21, 2022 10:45:11 AM
In a recent survey conducted by IBM’s Institute of Business Value, more than 14,000 respondents voiced their opinions about a hybrid work model. The survey results portray a shift in employee expectations with their employers and an emphasis on greater work-life balance along with hybrid work flexibility. In today’s hyper-competitive job market, many organizations are looking at a hybrid work model to retain and recruit top talent while streamlining their operations. For IT organizations making the shift from in-office work to a hybrid workforce, this idea may sound a bit daunting. For those individuals, Versatile’s team of experts put together a few tips & tricks to help you with your transition into a secure and flexible hybrid work model.
Microsoft’s New Commerce Experience and How it Affects You
By Greg Marts on Mar 8, 2022 9:43:48 AM
When Microsoft launched their New Commerce Experience (NCE), its goal was to provide customers greater choice and flexibility with license purchasing. For the past 10 years, licensees had the option to cancel anytime without penalty, add or reduce seats as required, pay per day, or choose annual terms for seat-based offers in the Microsoft Cloud Solution Provider (CSP) Program.
Staying Safe & Secure for the New Year
By Greg Marts on Jan 5, 2022 2:16:15 PM
Stay safe this new year and secure yourself and your loved ones online with these ten tips from our cloud expert.
Creating flexible, modern, creative work environments
By John Barker on Dec 8, 2021 4:01:47 PM
Versatile has reinforced its commitment to creating the most flexible, modern, and creative work environment by moving our headquarters from Marlboro to Hudson, MA!
Age of Web Conferencing: Benefits of Switching to Online
By Greg Marts on Mar 26, 2020 9:15:00 AM
Even before the Covid-19 outbreak many businesses were not fully leveraging what we consider to be one of the most invaluable tools in your organization.
Tips & Tricks to Optimize Productivity While Working From Home
By The Versatile Team on Mar 25, 2020 9:08:00 AM
Due to the outbreak of Covid-19 many workers have been sent home to work to help prevent the spread of the virus.
Protecting Clinical Care Endpoints from Cyber Attacks
By Afzal Bashir on Feb 5, 2020 10:20:03 PM
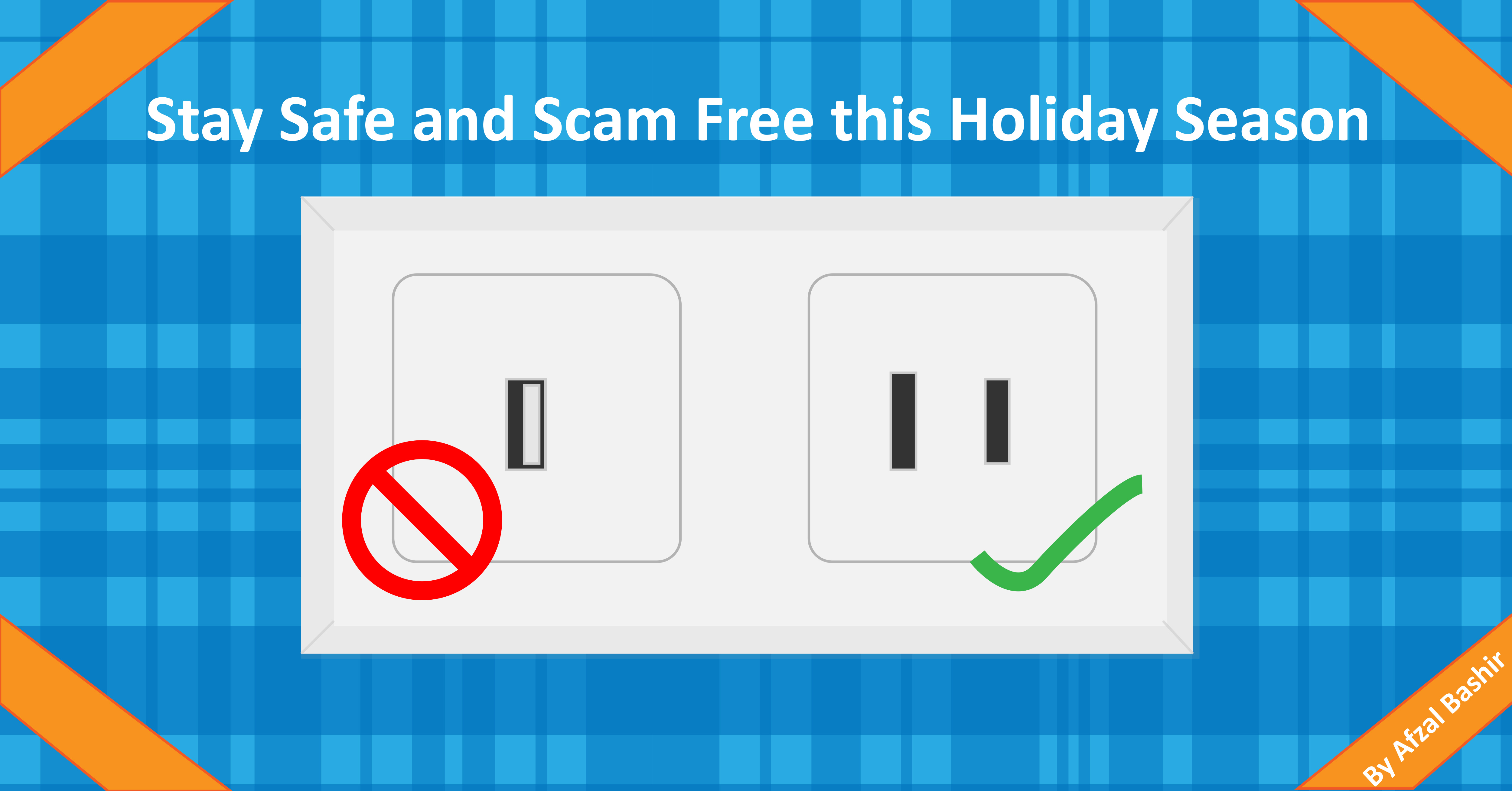
Staying Safe and Scam Free this Holiday Season
By Afzal Bashir on Nov 27, 2019 3:27:02 PM
Thanks to technology we can now connect in so many ways but, this also means hackers have found a way to grinch up the holidays by being able to download your information from a simple charging station. Follow these simple tips to keep your personal and company’s data from hackers this holiday season!
Overcoming the Challenges of Clinical Care Computing
By Andrew Ruth on Nov 26, 2019 10:32:51 AM
Over the past few years, the healthcare computing environment has changed dramatically. Driven as much by new opportunities for innovation as by security threats to data and operations, the pace of change is only likely to accelerate in the years ahead. Keeping up with these changes is no longer just an issue of ideal optimization, it's a matter of survival for many healthcare organizations whether they recognize the risk or not.